Read more of this story at Slashdot.
In this episode of the PowerShell Podcast, I'm joined by Ryan Lancial - Security Engineer at Red Canary. We talk about our shared history, his journey to security, what makes a good company culture, succeeding with no degree, the value of authenticity, and more!
Guest Bio and links:
Ryan Lancial hates bios, used to Powershell and admin and now talks about security.
PowerShell Podcast Home page: https://www.pdq.com/resources/the-powershell-podcast/
https://www.linkedin.com/in/ryanlancial/
PowerShell Pro Tips - https://www.youtube.com/watch?v=K95ovoMh170
https://www.pdq.com/blog/what-are-rest-apis/
https://woshub.com/read-outlook-email-powershell/
https://blog.danskingdom.com/PowerShell-DevOps-Global-Summit-2024-reflections/
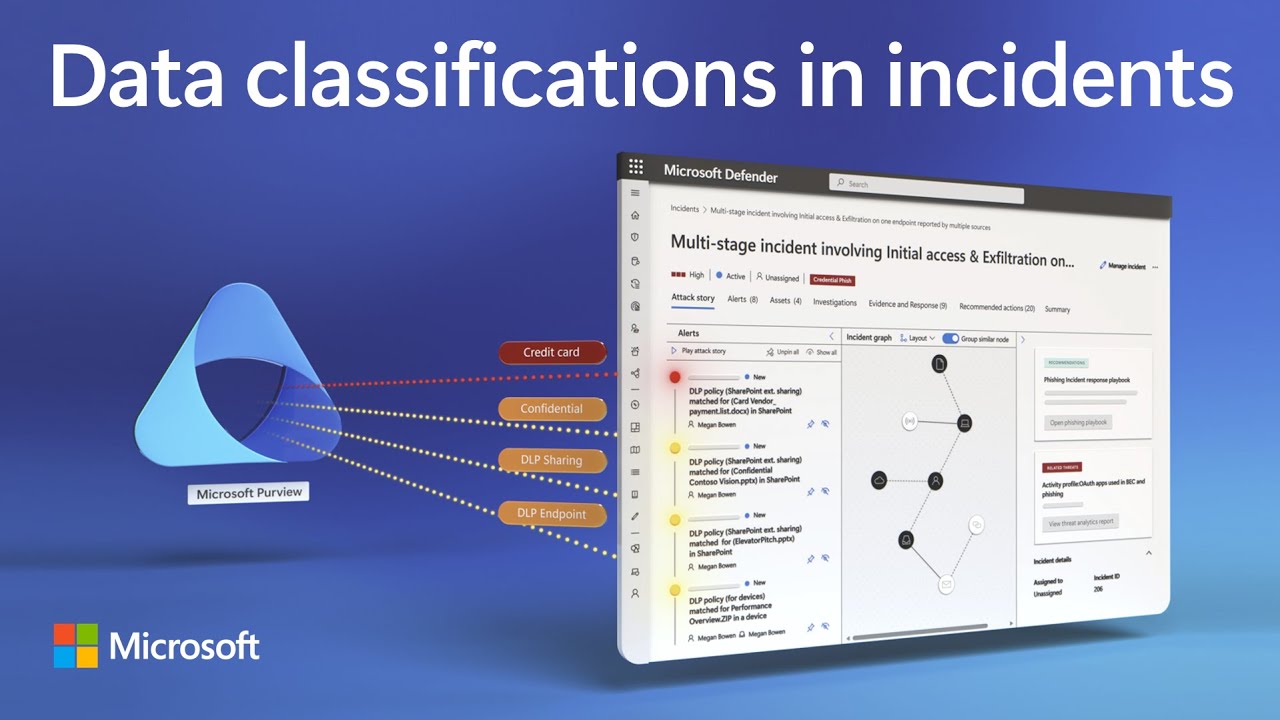
Prioritize incidents based on data significance, detect insider risks, and adapt protections in real-time with Microsoft Defender XDR and Microsoft Purview. Customize thresholds and risk indicators to detect anomalous behavior and prevent potential breaches with Adaptive Protection. Receive real-time DLP alerts triggered by policy matches, ensuring immediate action to safeguard sensitive data. Gain comprehensive visibility into threats and enforce policies across all devices and applications.
Sravan Kumar Mera, Principal Product Manager for Microsoft Purview shares how to stay ahead of evolving threats and maintain data integrity.
► QUICK LINKS:
00:00 - Prioritize security incidents based on data importance
00:42 - High severity multistage incident
01:29 - DLP alerts
02:24 - Insider risk activity summary
03:30 - Set up data security foundation
04:47 - Adaptive Protection
05:50 - DLP policy & Conditional Access
06:33 - Wrap up
► Link References
Get started at https://purview.microsoft.com
Watch our data security playlist at https://aka.ms/datasecuritymechanics
► Unfamiliar with Microsoft Mechanics?
As Microsoft's official video series for IT, you can watch and share valuable content and demos of current and upcoming tech from the people who build it at Microsoft.
• Subscribe to our YouTube: https://www.youtube.com/c/MicrosoftMechanicsSeries
• Talk with other IT Pros, join us on the Microsoft Tech Community: https://techcommunity.microsoft.com/t5/microsoft-mechanics-blog/bg-p/MicrosoftMechanicsBlog
• Watch or listen from anywhere, subscribe to our podcast: https://microsoftmechanics.libsyn.com/podcast
► Keep getting this insider knowledge, join us on social:
• Follow us on Twitter: https://twitter.com/MSFTMechanics
• Share knowledge on LinkedIn: https://www.linkedin.com/company/microsoft-mechanics/
• Enjoy us on Instagram: https://www.instagram.com/msftmechanics/
• Loosen up with us on TikTok: https://www.tiktok.com/@msftmechanics
#MicrosoftPurview #MicrosoftDefender #XDR #DataSecurity
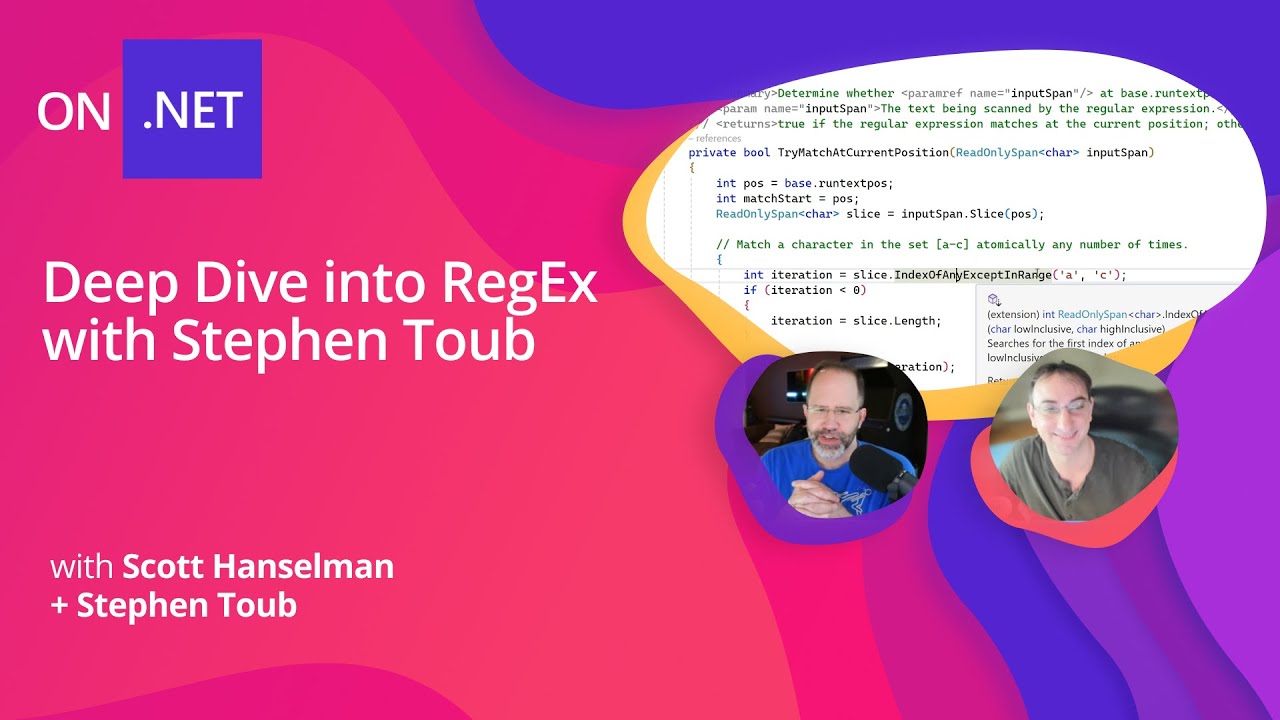
Scott and Stephen are back with another deep dive into C# and .NET features. This time is RegEx, everyone's favorite powerful magical strings that you can never figure out how to exactly get write. Stephen breaks down every bit that you need to know about RegEx in .NET.
Chapters:
00:00:00 Understanding and Utilizing Regular Expressions in Software Development
00:04:36 Deep Dive into Regular Expressions in Visual Studio
00:11:22 Understanding Regular Expressions and Their Applications
00:17:20 Understanding the Interpretation and Implementation of Regular Expressions in Programming
00:18:22 Understanding the Process of Programming: Interpretation and Compiling
00:23:48 Exploring New Engine Features in .NET 7
00:26:49 Understanding the Role and Functionality of Source Generators in the C# Project
00:31:33 Understanding the Role and Functionality of Source Generators in Programming
00:33:23 Discussing the Functionality and Evolution of Source Generators in C#
00:37:03 Discussing Testing and Debugging Regular Expressions
00:40:08 Understanding the Algorithmic Process of Matching Patterns
00:42:28 Understanding the Complexity and Backtracking in Linear Programming
00:43:30 Understanding the Complexity and Efficiency of Regular Expressions
00:50:29 Exploring the Efficiency and Limitations of Regex Engines in Web Development
00:54:24 Discussion on Regex Implementation and Caching in Programming
00:57:58 Exploring the Implementation and Best Practices of Regular Expressions in Application Development
01:02:39 Understanding the Use of Search Values in .NET 8 and its Optimization
01:04:31 Understanding the Internals of Regex Programming
Resources:
Docs: https://learn.microsoft.com/dotnet/standard/base-types/regular-expression-language-quick-reference
Connect with .NET:
Blog: https://aka.ms/dotnet/blog
Twitter: https://aka.ms/dotnet/twitter
TikTok: https://aka.ms/dotnet/tiktok
Mastodon: https://aka.ms/dotnet/mastodon
LinkedIn: https://aka.ms/dotnet/linkedin
Facebook: https://aka.ms/dotnet/facebook
Docs: https://learn.microsoft.com/dotnet
Forums: https://aka.ms/dotnet/forums
🙋♀️Q&A: https://aka.ms/dotnet-qa
👨🎓Microsoft Learn: https://aka.ms/learndotnet
#dotnet #csharp #regex
Guest:
-
Elie Bursztein, Google DeepMind Cybersecurity Research Lead, Google
Topics:
-
Given your experience, how afraid or nervous are you about the use of GenAI by the criminals (PoisonGPT, WormGPT and such)?
-
What can a top-tier state-sponsored threat actor do better with LLM? Are there “extra scary” examples, real or hypothetical?
-
Do we really have to care about this “dangerous capabilities” stuff (CBRN)? Really really?
-
Why do you think that AI favors the defenders? Is this a long term or a short term view?
-
What about vulnerability discovery? Some people are freaking out that LLM will discover new zero days, is this a real risk?
Resources:
-
“How Large Language Models Are Reshaping the Cybersecurity Landscape” RSA 2024 presentation by Elie (May 6 at 9:40AM)
-
“Lessons Learned from Developing Secure AI Workflows” RSA 2024 presentation by Elie (May 8, 2:25PM)
-
EP50 The Epic Battle: Machine Learning vs Millions of Malicious Documents
-
EP170 Redefining Security Operations: Practical Applications of GenAI in the SOC
-
EP168 Beyond Regular LLMs: How SecLM Enhances Security and What Teams Can Do With It
-
Threat Actors are Interested in Generative AI, but Use Remains Limited
Download audio: https://traffic.libsyn.com/secure/cloudsecuritypodcast/EP171_not170_CloudSecPodcast.mp3?dest-id=2641814
Ready for a tech world where you can fix what you own? Join us as we celebrate the Right to Repair movement, and push for a more sustainable and consumer-friendly future.
We'll explore why repairing should be easy, affordable, and a joyful act of ownership and how Google is driving meaningful changes in legislation to support a consumer's right to repair.
We'll uncover the hidden potential of the things we already have and how fixing them ourselves empowers us. Plus, we'll spotlight a tech leader changing the game: Google's Pixel. Learn how Pixel is being designed from the ground up to make its phones easier to repair and help usher in a new era of repairable tech.
Hosted on Acast. See acast.com/privacy for more information.
Download audio: https://sphinx.acast.com/p/open/s/63e39eb02e631f0011a284ac/e/663393aae9604e0012e05efe/media.mp3